Cloud volume block storage now available in Cluj
Cloud volumes block storage is now available in the Cluj region.

Cloud volumes block storage is now available in the Cluj region.

On June 26th cPanel announced licensing model changes and price increases. The cPanel license no longer includes unlimited cPanel accounts, it is based on the number of cPanel accounts you have on your server. We’re updating our cPanel licensing prices to reflect this change.

We’re happy and excited to announce that after 10 years we’re back in Cluj-Napoca, our home town.

Recently there’s been a significant and unexpected change in the web hosting industry. cPanel announced a considerable price increase that affects especially web hosting reseller accounts and VPS owners.
We did our best in these the last two crazy days and come to a deal with the friendly people at DirectAdmin.

Anyone need more RAM? One can never have enough RAM… as @thezedt was tweeting.
We have just doubled the memory (RAM) included in our VPS packages without any price increase.

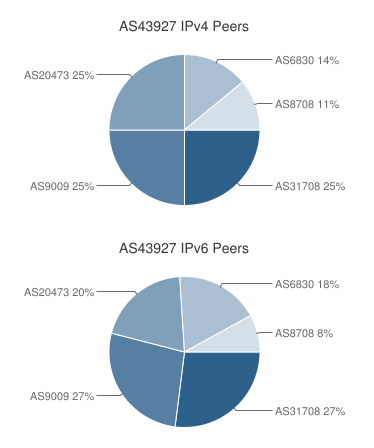 If you’re a RIPE member and have your own IP prefix(es), you can bring your own IP addresses and we’ll announce them from our AS number. The service is available in Bucharest and London. In the following months it will also be available in Dallas and Fremont.
If you’re a RIPE member and have your own IP prefix(es), you can bring your own IP addresses and we’ll announce them from our AS number. The service is available in Bucharest and London. In the following months it will also be available in Dallas and Fremont.
We can announce IPv4 and IPv6 for you.
You can use the IP addresses on the IntoVPS unmanaged VPS plans or on our managed VPS plans. Contact us if you’re looking for dedicate servers.
This service is free if charge. Data traffic will be charged at usual rates.
On your request we’ve introduced a lowered price 1GB RAM VPS. As all our VPS plans, it has a full-SSD storage and cost tracked per hour.
Our new KVM VPS’es platform, powered by Fleio and OpenStack, is now available in Dallas and Fremont.
You get the same benefits as in the previously opened locations (Amsterdam and Bucharest):
The virtual machines cost starts at one cent and half per hour for 2GB of RAM.
And some useful add-ons are available for the virtual machines:
The new platform will soon be available in London too.
This is a long, looong awaited feature:
You can get a Windows Server 2016 Standard virtual machine with 2 GB of RAM for 2 cents per hour.
The Windows instances have the same, fast local SSD storage.
The current locations available are Amsterdam and Bucharest with more to come soon.
Today we are launching our new OpenStack based platform powered by Fleio.