DirectAdmin now free with all accounts
Recently there’s been a significant and unexpected change in the web hosting industry. cPanel announced a considerable price increase that affects especially web hosting reseller accounts and VPS owners.
We did our best in these the last two crazy days and come to a deal with the friendly people at DirectAdmin.


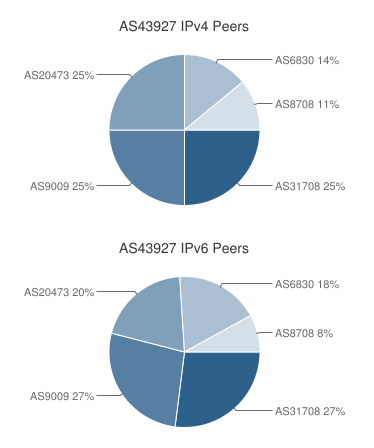 If you’re a RIPE member and have your own IP prefix(es), you can bring your own IP addresses and we’ll announce them from our
If you’re a RIPE member and have your own IP prefix(es), you can bring your own IP addresses and we’ll announce them from our